Welcome to Pyramid IT Solutions
Pyramid IT Solutions is a leading end-to-end service provider of IT Solutions encompassing Design, Implementation, Configuration and Management of IT Infrastructure. We specialize in the field of Wired, Wireless, Optical fiber Installation & Management services for small, medium and large campus Networks. We are one of the fast-track growing Networking Company based at Hyderabad with extended operations in Pune, Bangalore & Visakhapatnam.
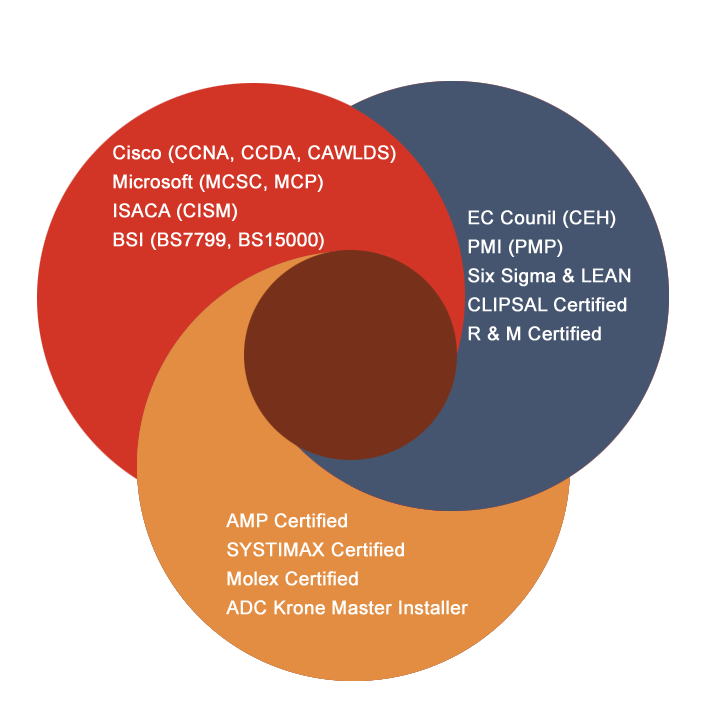
Pyramid has established its expertise in IT Services by efficiently providing customer-centric services to several small, medium and large organizations in India by the help of technically qualified professionals. Conscious efforts from Pyramid in building the technical skills have helped us in growing our business and serving our esteemed customers. We possess skill in various technologies viz. Microsoft, Cisco, Juniper, Forte gate, D-Link, SYSTIMAX, AMP, and Clipsal.
READ MORE
<div data-id="741a32a0" class="elementor-element elementor-element-741a32a0
<div data-id="a814b8" class="elementor-element elementor-element-a814b8
<div data-id="76265e7e" class="elementor-element elementor-element-76265e7e elementor-column elementor-col-50